Cross-Enterprise User Assertion (XUA) Profile: Difference between revisions
JohnMoehrke (talk | contribs) No edit summary |
JohnMoehrke (talk | contribs) No edit summary |
||
| Line 1: | Line 1: | ||
=Introduction= | =Introduction= | ||
''This is a draft of the | ''This is a draft of the Cross-Enterprise User Assertion Profile (XUA) supplement to the ITI Technical Framework. This draft is a work in progress, not the official supplement or profile.'' | ||
__TOC__ | __TOC__ | ||
==Profile Abstract== | ==Profile Abstract== | ||
The | The Cross-Enterprise User Assertion Profile (XUA) provides a trustable user identity for transactions that cross enterprise boundaries. The user identities may be centrally managed, or distributed. | ||
==Glossary== | ==Glossary== | ||
; | ; XUA : Cross-Enterprise User Assertion (Formerly Cross-Enterprise User Authentication) | ||
==Issue Log== | ==Issue Log== | ||
===Open Issues=== | ===Open Issues=== | ||
| Line 14: | Line 15: | ||
# Issue | # Issue | ||
===Closed Issues=== | ===Closed Issues=== | ||
=Volume I= | =Volume I= | ||
<pre>Add the following bullet to the list of profiles</pre> | <pre>Add the following bullet to the list of profiles</pre> | ||
* | * Cross-Enterprise User Assertion - provides a trustable user identity for transactions that cross enterprise boundaries. This user assertion carries information about the methods used to authenticate the user, and attributes about the user. The service consuming this user assertion may use the information in the user assertion for access control, auditing, or other purposes. The user identities may be centrally managed, or distributed. | ||
===Dependencies=== | ===Dependencies=== | ||
| Line 26: | Line 28: | ||
!Purpose | !Purpose | ||
|- style='background-color:#ffffff;' align='center' | |- style='background-color:#ffffff;' align='center' | ||
| | |Cross-Enterprise User Assertion | ||
| | | | ||
| | | | ||
| Line 33: | Line 35: | ||
|} | |} | ||
==Profile Name== | ==Profile Name== | ||
The | The Cross-Enterprise User Assertion Profile (XUA) provides a trustable user identity for transactions that cross enterprise boundaries. The user identities may be centrally managed, or distributed. | ||
There are transactions defined by IHE that cross enterprise boundaries. The existing IHE mechanisms to provide an authenticated user identity (EUA) will not function in cross-enterprise transactions. Further in a cross-enterprise environment it is more likely that the transactions will be going between two enterprises that maintain their own independent user directories (PWP). This problem is the same focus of the OASIS-SAML standard. This standard has received much attention and support by the security and the platforms industry. This standard allows for centralized user directory, but also supports the more powerful federation of user directories. This standard supports many methods of user authentication (password, biometrics, smartcard) and can include details about the method(s) used. | |||
The solution proposed is to leverage SAML and the various profiles from [http://www.w3c.org W3C], [http://www.oasis-open.org OASIS], and [http://www.ws-i.org WS-I]. In this way we will be able to take advantage of the vast experience of the communities outside of healthcare standards. This profile will be leveraging the experience of a few programs around the globe that have started work with SAML in healthcare. Most of these projects are applying SAML to XDS as we expect to be doing in the first year. | |||
Discussion about the creation of this profile can be found at [[Cross-Enterprise User Assertion - Discussion]] | |||
===Use Cases=== | ===Use Cases=== | ||
This profile will likely take two years to fully fill out. In the first year we will be focusing only on the consumption side of XDS, specifically the Registry Stored Query and Retrieve Document transactions. The motivator for this is that these are the most exposed transactions that IHE has defined; their use is expected to be from a wide variety of consuming applications and enterprises. | |||
# General practice doctor retrieving results of a test performed by an outpatient clinic. | |||
# Outpatient clinic retrieving request to perform a test and background information necessary. | |||
# Doctor in an emergency situation request to retrieve documents (that would under normal conditions would not be accessible) | |||
## Where the privacy consent (BPPC) has restricted access | |||
# System, based on a scheduled procedure, pre-fetches the available documents so that it can determine a relevant few documents to offer to the doctor when the patient arrives. | |||
# Patient, using a PHR like application, accesses their own information in XDS. | |||
# Access of a document by an individual that can’t be identified because the SAML-IDP (X-Assertion Provider) is not accessible | |||
===Actors/Transaction=== | ===Actors/Transaction=== | ||
[[image:at.jpg|frame|center| | [[image:at.jpg|frame|center|Cross-Enterprise User Assertion Actor Diagram]] | ||
{|style='background-color:#7f7f7f;' align='center' border='1' cellspacing='0' | {|style='background-color:#7f7f7f;' align='center' border='1' cellspacing='0' | ||
| Line 52: | Line 62: | ||
!Opt. | !Opt. | ||
!Section | !Section | ||
|+ | |+Cross-Enterprise User Assertion Actors and Transactions | ||
|- style='background-color:#ffffff;' align='center' | |- style='background-color:#ffffff;' align='center' | ||
|Actor 1 | |Actor 1 | ||
| Line 81: | Line 91: | ||
=== Process Flow === | === Process Flow === | ||
[[Image:seq.jpg|frame|center| | [[Image:seq.jpg|frame|center|Cross-Enterprise User Assertion Process Flow]] | ||
More text about process flow | More text about process flow | ||
== Actor Definitions == | == Actor Definitions == | ||
* [[X-Assertion Provider]] – This is a SAML Identity Provider (IDP), and is not further specified by IHE. | |||
* [[X-Service User]] – This is the system making a web-services request. In the first year this is the XDS-Document Consumer Actor. | |||
* [[X-Service Provider]] – This is the system providing the web-service. In the first year this is the XDS-Document Registry and XDS-Document Repository Actors. | |||
== Transaction Definitions == | == Transaction Definitions == | ||
; Transaction : Definition | ; Transaction : Definition | ||
Revision as of 18:52, 29 March 2007
Introduction
This is a draft of the Cross-Enterprise User Assertion Profile (XUA) supplement to the ITI Technical Framework. This draft is a work in progress, not the official supplement or profile.
Profile Abstract
The Cross-Enterprise User Assertion Profile (XUA) provides a trustable user identity for transactions that cross enterprise boundaries. The user identities may be centrally managed, or distributed.
Glossary
- XUA
- Cross-Enterprise User Assertion (Formerly Cross-Enterprise User Authentication)
Issue Log
Open Issues
- Issue
- Issue
Closed Issues
Volume I
Add the following bullet to the list of profiles
- Cross-Enterprise User Assertion - provides a trustable user identity for transactions that cross enterprise boundaries. This user assertion carries information about the methods used to authenticate the user, and attributes about the user. The service consuming this user assertion may use the information in the user assertion for access control, auditing, or other purposes. The user identities may be centrally managed, or distributed.
Dependencies
Add the following row(s) to the list of dependencies
| Integration Profile | Dependency | Dependency Type | Purpose |
|---|---|---|---|
| Cross-Enterprise User Assertion |
Profile Name
The Cross-Enterprise User Assertion Profile (XUA) provides a trustable user identity for transactions that cross enterprise boundaries. The user identities may be centrally managed, or distributed.
There are transactions defined by IHE that cross enterprise boundaries. The existing IHE mechanisms to provide an authenticated user identity (EUA) will not function in cross-enterprise transactions. Further in a cross-enterprise environment it is more likely that the transactions will be going between two enterprises that maintain their own independent user directories (PWP). This problem is the same focus of the OASIS-SAML standard. This standard has received much attention and support by the security and the platforms industry. This standard allows for centralized user directory, but also supports the more powerful federation of user directories. This standard supports many methods of user authentication (password, biometrics, smartcard) and can include details about the method(s) used.
The solution proposed is to leverage SAML and the various profiles from W3C, OASIS, and WS-I. In this way we will be able to take advantage of the vast experience of the communities outside of healthcare standards. This profile will be leveraging the experience of a few programs around the globe that have started work with SAML in healthcare. Most of these projects are applying SAML to XDS as we expect to be doing in the first year.
Discussion about the creation of this profile can be found at Cross-Enterprise User Assertion - Discussion
Use Cases
This profile will likely take two years to fully fill out. In the first year we will be focusing only on the consumption side of XDS, specifically the Registry Stored Query and Retrieve Document transactions. The motivator for this is that these are the most exposed transactions that IHE has defined; their use is expected to be from a wide variety of consuming applications and enterprises.
- General practice doctor retrieving results of a test performed by an outpatient clinic.
- Outpatient clinic retrieving request to perform a test and background information necessary.
- Doctor in an emergency situation request to retrieve documents (that would under normal conditions would not be accessible)
- Where the privacy consent (BPPC) has restricted access
- System, based on a scheduled procedure, pre-fetches the available documents so that it can determine a relevant few documents to offer to the doctor when the patient arrives.
- Patient, using a PHR like application, accesses their own information in XDS.
- Access of a document by an individual that can’t be identified because the SAML-IDP (X-Assertion Provider) is not accessible
Actors/Transaction
| Actor | Transaction | Opt. | Section |
|---|---|---|---|
| Actor 1 | Transaction 1 | R | #Transaction 1 |
Options
| Actor | Option | Section |
|---|---|---|
| Actor 1 | Option 1 | #Option 1 |
Option 1
A description of option 1.
Grouping
Process Flow
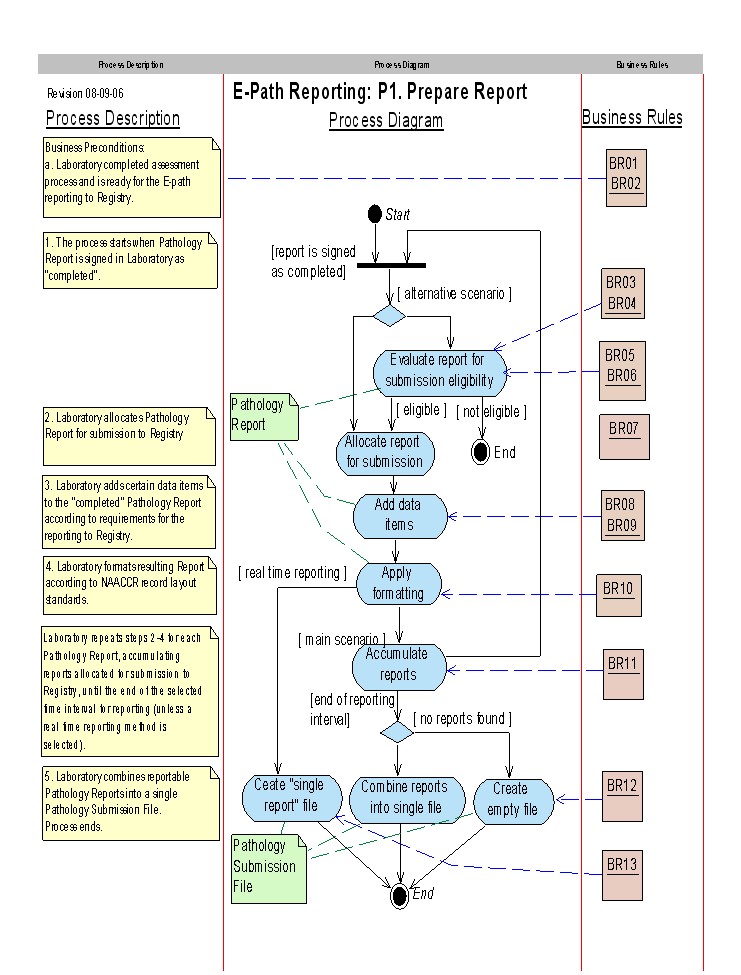
More text about process flow
Actor Definitions
- X-Assertion Provider – This is a SAML Identity Provider (IDP), and is not further specified by IHE.
- X-Service User – This is the system making a web-services request. In the first year this is the XDS-Document Consumer Actor.
- X-Service Provider – This is the system providing the web-service. In the first year this is the XDS-Document Registry and XDS-Document Repository Actors.
Transaction Definitions
- Transaction
- Definition
Volume II
Transaction 1
Scope
Use Case Roles
[[image:ucr.jpr|frame|center]
- Actor
- Actor 1
- Role
- Role of Actor 1
lather, rise and repeat for each actor
Referenced Standards
- STD
- Description